September 20, 2011
NetworkMiner, Network Forensic Analysis Tool for Windows
Do you like this story?
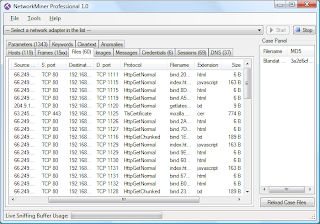
NetworkMiner is a Network Forensic Analysis Tool (NFAT) for Windows. NetworkMiner can be used as a passive network sniffer/packet capturing tool in order to detect operating systems, sessions, hostnames, open ports etc. without putting any traffic on the network. NetworkMiner can also parse PCAP files for off-line analysis and to regenerate/reassemble transmitted files and certificates from PCAP files.
NetworkMiner collects data (such as forensic evidence) about hosts on the network rather than to collect data regarding the traffic on the network. The main user interface view is host centric (information grouped per host) rather than packet centric (information showed as a list of packets/frames).
NetworkMiner can extract files and certificates transferred over the network by parsing a PCAP file or by sniffing traffic directly from the network. This functionality can be used to extract and save media files (such as audio or video files) which are streamed across a network from websites such as YouTube. Supported protocols for file extraction are FTP, TFTP, HTTP and SMB.
NetworkMiner has, since the first release in 2007, become popular tool among incident response teams as well as law enforcement
The new version supports features such as:
NetworkMiner_1-1.zip
NetworkMiner collects data (such as forensic evidence) about hosts on the network rather than to collect data regarding the traffic on the network. The main user interface view is host centric (information grouped per host) rather than packet centric (information showed as a list of packets/frames).
NetworkMiner can extract files and certificates transferred over the network by parsing a PCAP file or by sniffing traffic directly from the network. This functionality can be used to extract and save media files (such as audio or video files) which are streamed across a network from websites such as YouTube. Supported protocols for file extraction are FTP, TFTP, HTTP and SMB.
NetworkMiner has, since the first release in 2007, become popular tool among incident response teams as well as law enforcement
The new version supports features such as:
- Extraction of Google Analytics data
- Better parsing of SMB data
- Support for PPP frames
- Even more stable than the 1.0 release
NetworkMiner_1-1.zip
 About the Author:
Ifeanyi Emeka is the founder of this blog and also writes for Tech Forked. He is passionate about tech stuffs and loves customizing blogger themes.
About the Author:
Ifeanyi Emeka is the founder of this blog and also writes for Tech Forked. He is passionate about tech stuffs and loves customizing blogger themes.Popular This Week
NetworkMiner, Network Forensic Analysis Tool for Windows
2011-09-20T18:34:00+01:00
dfgdfg
Hacking Tools|Network forensics|Packet sniffers|
Subscribe to:
Post Comments (Atom)